A nice adapter that has both input and output is this which i got from AliExpress (Photos at the bottom)
This 4K dummy adapter seems to support all resolutions up to 60Hz refresh rate, with the exception of 4K which works at a maximum of 30Hz (Probably due to signal attenuation)
There are many uses for this dummy adapter, one of them is “Sunshine and moonlight remote desktop”, another is using your GPU for processing while you are away (Nvidia won’t allow it if you don’t have a monitor connected and switched on), and most importantly TO ME, My video switch since I use multiple machines on the same monitor.
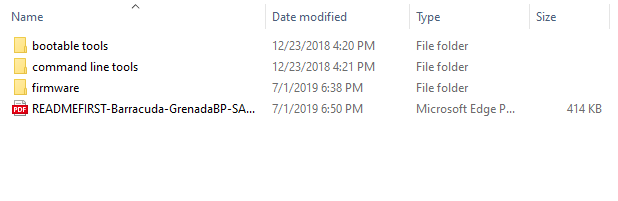
What this adapter is in reality is an eeprom chip that has the EDID data of a monitor with a very high refresh rate (120 hz), namely a fictitious monitor named AOC 28E850, If you want to make sure that this works with your monitor, it needs to be flashed with your monitor’s EDID.
If your monitor supports 4K at 60hz, you need to keep everything in that copy, and remove the 4K.60Hz from the list
If you want the modified file that originated from my LG 27UL550 and was modified to remove the 60Hz from the list of supported configurations, meaning I removed the 60 FPS from the 4K DTD, then here it is, just download it and flash it (Flashing instructions below) I also changed the monitor’s name just in case some systems might cache it’s details…
The steps
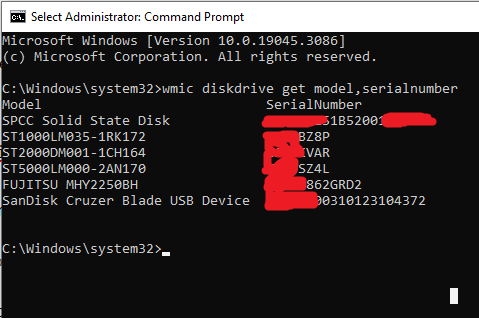
1- Find out the port on your graphics card that your monitor is connected to
2- Copy the EDID data from your monitor
3- Edit the data to remove the 4K/60 fps
4- Burn the data onto the adapter
To do that, there are many tools, one thing to note is that edid-rw did not work using my laptop which has a 9400mx, but worked just fine using an old PC i have with a “GT218 [GeForce 210]”, the error on the laptop reads
sudo ./edid-rw 5
Traceback (most recent call last):
File “./edid-rw”, line 131, in
main()
File “./edid-rw”, line 119, in main
edid = [dev.read(i) for i in range(EDID_HDR)]
File “./edid-rw”, line 46, in read
return self.smb.read_byte_data(EDID_ADDR, n)
IOError: [Errno 110] Connection timed out
edid-rw tool: https://github.com/bulletmark/edid-rw
wxedid tool: install from debian repo
I personally used the tools above to read/write/edit, but if you have access to a windows machine, AW-EDID should be the best tool for editing….
Analog Way EDID editor: https://www.analogway.com/apac/products/software-tools/aw-edid-editor/
So, let’s get down to that voodoo business !
1- There seems to be a very cool python script (tool) called edid-rw, let us install it’s prerequisites
sudo apt-get install python3-smbus edid-decode git
Now, you have python, let us download the tool, you can do that with the download button on github, I would rather just
git clone https://github.com/bulletmark/edid-rw
cd edid-rw
To begin with, you may need to run the following command to see what monitors are connected where, In my case, the monitor I want to copy (LG 4K 60FPS) is #5
xrandr --query
If this does not help, try the numbers and read the output to see which entry corresponds to the screen you want
sudo ./edid-rw 5 | edid-decode
Now that we have it, we can edit it with one of the software mentioned above, and dump it back on the dongle (The port number does not change, so put your number there and dump the data onto it)
udo ./edid-rw -w 5 < ~/edited_lgedid.bin
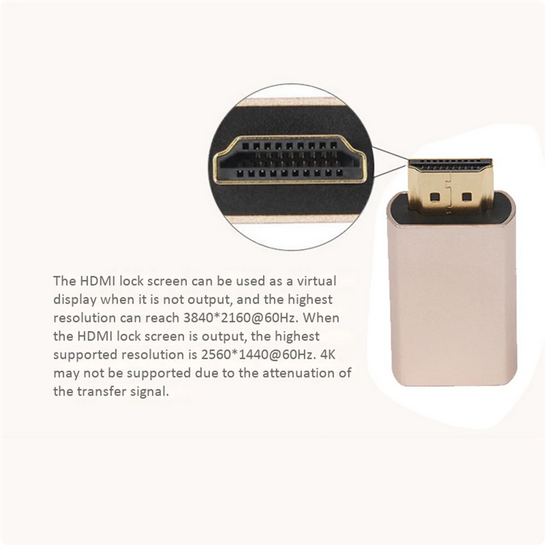

Text from the original page of the item
Support hot plug, plug and play
Support virtual display, when the display is powered off or the display cable is hot-plugged, It can achieve no video signal loss, no screen change, no windows running, no order disorder;
Support up to 10.8Gbps video bandwidth; It has power-off memory function, power-off/restart display sequence is not chaotic, and the set mode is not lost.
Supports for AMD multi-screen image card splicing extended split-screen mode, eyefinity wide-area multi-screen splicing mode (pulling the monitor cable when it is powered on has no effect on the display of the screen TV wall, and pulling the line will only cause the screen of the dropped line to be black, and other screens will not move)
Support Nvidia image card multi-screen output, the screen sequence is not chaotic after restart
Connect typ:HDMI
Application scope: Display with HDMI interface
Product name :HDMI lock screen treasure
Max Resolution : 2560 x 1440@60HZ / 3840 x 2160@60HZ
colour:Golden
Material:Aluminum alloy
Package Contents:
6 x HDMI2.0 Virtual Adapter
The aluminum sleeve appears to be fully cosmetic, At least this is my impression as the plastic inside seems very hard, so it is unlikely that the aluminum is providing any support, and obviously is not functioning as any form of heat sink